
Phishing Campaign Exploiting QR Codes: A Threat to US Energy Company
Discover how a large-scale phishing campaign using QR codes targeted a major US energy company, stealing Microsoft credentials. Learn about the unique tactics employed by cybercriminals and essential defense strategies against QR code-based attacks.

Discord.io Data Breach: 760,000 Members' Data Stolen – How to Protect Yourself
Learn about the recent Discord.io data breach affecting 760,000 members. Understand the implications, steps taken, and how to safeguard your account and data.

Alarming Surge in LinkedIn Account Hacking and How to Protect Yourself
Discover an alarming trend of LinkedIn account hacking, as revealed by the Cyberint research team. Uncover the attack method, impact on victims, and preventive measures to safeguard your professional identity.

Critical Vulnerabilities in Ivanti Avalanche: A Deep Dive
Learn about critical vulnerabilities in Ivanti Avalanche's WLAvanacheServer.exe v6.4.0.0 discovered by Tenable researchers. Explore the intricacies of stack-based buffer overflows, their potential impact, and the swift mitigation steps taken.

Unveiling the Underground: Insights into Cybercrime Forums from Info-Stealer Infections
Explore the dark world of cybercrime forums and info-stealer infections with Hudson Rock's revealing insights. Discover compromised computers, unmasked hackers, forum credentials, and the surge in cyber threats.

Unveiling PyPI's Hidden Dangers: The Rising Tide of Zero-Day Attacks
Discover the growing threat of zero-day attacks on Python Package Index (PyPI) packages. Learn how cybercriminals exploit unsuspecting developers and explore the AI-powered defense mechanisms that are reshaping the fight against open-source supply chain attacks.

Unveiling the Sophisticated World of CryptoRom Scams: A Multi-Tiered Approach
Explore the sophisticated world of CryptoRom scams, where fake cryptocurrency trading meets feigned romance. Discover how scammers utilize generative AI, infiltrate legitimate app stores, and escalate their tactics to extract more money from victims. Learn how victims can take action, report incidents, and raise awareness to counter this growing menace.

Police Take Down Lolek Bulletproof Hosting Provider: Unmasking Cybercrime Facilitators
Learn about the takedown of Lolek bulletproof hosting provider and the arrest of five individuals for facilitating Netwalker ransomware attacks and other cybercrimes. Understand the role of bulletproof hosting in cybercriminal activities and the joint efforts of law enforcement to combat cyber threats.

Critical Vulnerabilities in Industrial Control Systems: A Closer Look at the Codesys Exploits
Learn about the recent vulnerabilities in Codesys' industrial control systems software that could potentially disrupt power plants and critical infrastructure. Understand the implications, exploits, and urgent actions required to mitigate these risks.

Navigating the Turmoil: Decoding Zoom's Terms of Service Changes and the Challenge of Legalese
Explore the recent changes in Zoom's Terms of Service (TOS) and the resulting controversy, shedding light on the challenges of deciphering complex legal language. Learn how user consent and AI integration play a role in the issue.

Unraveling Inception: A New Breed of Microarchitectural Attack on AMD CPUs
Discover the Inception attack, a groundbreaking microarchitectural exploit targeting modern AMD CPUs. Learn how the fusion of Phantom speculation and Training in Transient Execution enables unprivileged attackers to manipulate branch predictors, leak sensitive data, and the proposed mitigations.

New Malware Distribution Tactics: Freeze.rs and SYK Crypter Exploiting Rust Injector
Uncover the latest malware distribution tactics involving Rust injector "Freeze.rs" and "SYK Crypter." Learn how attackers exploit these tools to compromise devices, distribute malicious payloads, and collect sensitive information. Stay informed about evolving cyber threats and bolster your defenses against sophisticated attack chains.

Exploring VPN Vulnerabilities: Unmasking Cryptographic Flaws and Emerging Threats
Discover the latest research revealing vulnerabilities in Virtual Private Networks (VPNs). Learn about the Port Fail attack and WebRTC leak, which can compromise user privacy and expose real IP addresses. Explore practical solutions to enhance VPN security and safeguard against potential threats. Understand the importance of transparency and collaboration in addressing these vulnerabilities to ensure online privacy and protection.

Kubernetes Breaches: Unveiling Vulnerabilities and the Urgent Need for Security Measures
Discover the alarming truth about Kubernetes breaches as Aqua Security's research exposes over 60% of compromised clusters. Uncover the misconfigurations and vulnerabilities exploited by attackers, highlighting the urgent need for enhanced Kubernetes security measures.

EvilProxy: A Sophisticated Phishing Campaign Targets Microsoft 365 Accounts, Bypassing MFA
Explore the sophisticated EvilProxy phishing campaign targeting Microsoft 365 accounts and bypassing multi-factor authentication (MFA). Learn how attackers utilize brand impersonation, evasion techniques, and a reverse proxy framework to compromise high-ranking executives and steal sensitive data.

DARPA Launches AI Cyber Challenge to Revolutionize Software Security
Learn about the Downfall vulnerability in Intel CPUs, which exposes data isolation breaches and enables theft of sensitive information between applications. Explore its implications for cloud computing, its similarities to previous CPU vulnerabilities, Intel's response, and the challenge of balancing performance and security in chip design.
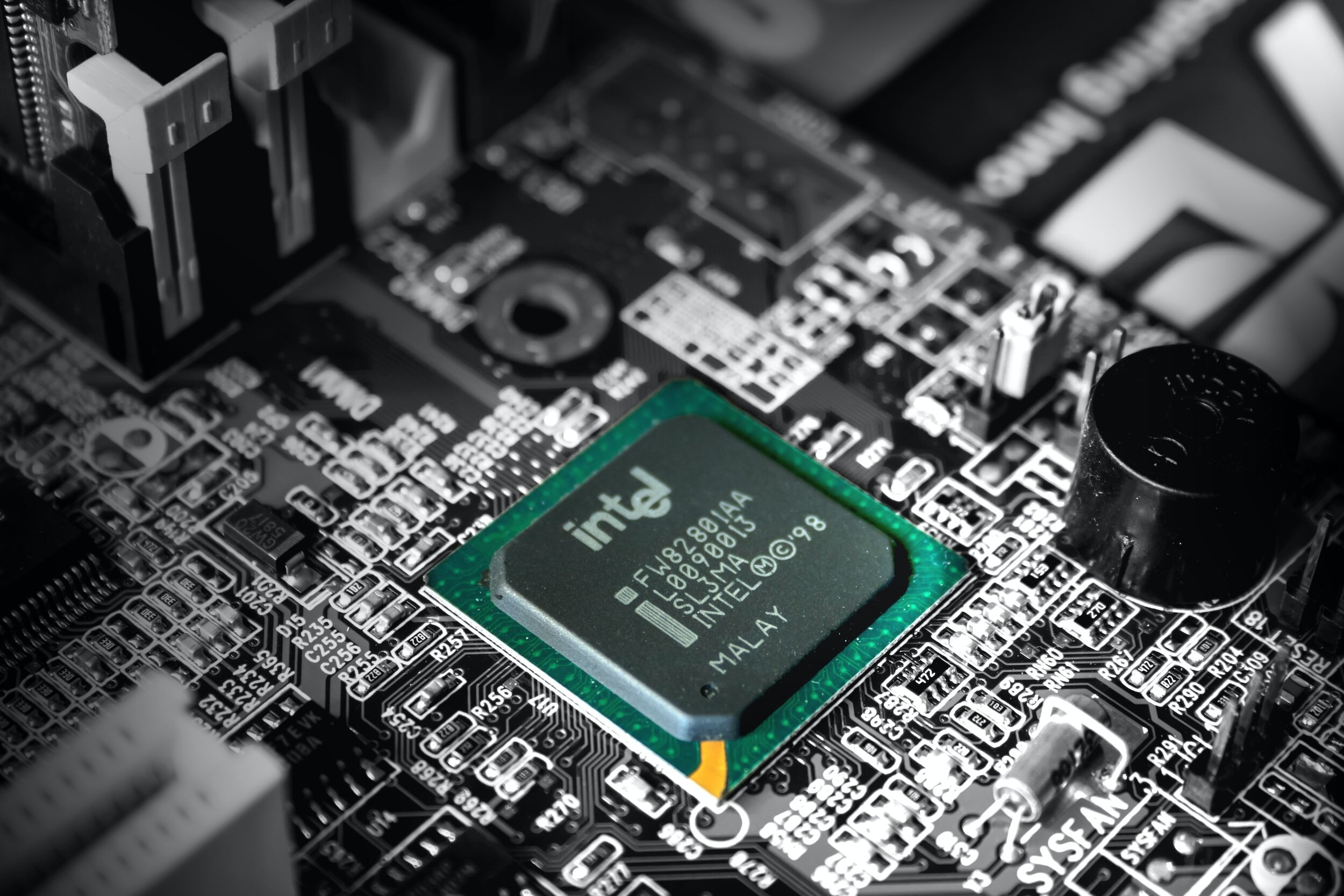
Downfall Vulnerability: A Deep Dive into Intel's Data Leak Threat
Learn about the Downfall vulnerability in Intel CPUs, which exposes data isolation breaches and enables theft of sensitive information between applications. Explore its implications for cloud computing, its similarities to previous CPU vulnerabilities, Intel's response, and the challenge of balancing performance and security in chip design.

The Rhysida Ransomware: Unveiling Connections and Tactics
Explore the connections and tactics of the Rhysida ransomware group and its ties to Vice Society. Learn about the striking parallels in their techniques, the rapid Time to Ransom (TTR), and their shared focus on targeting education and healthcare sectors.

Microsoft Fixes 74 CVEs in August Update: Protecting Against Active Exploitation and Diverse Threats
Stay informed about the latest Microsoft security update for August, addressing 74 vulnerabilities, including an active zero-day exploit. Learn how the update mitigates risks from remote code execution flaws, elevation of privilege bugs, and more, enhancing your organization's defense against evolving cyber threats.

Netgear NVRAM SSID-like Vulnerabilities Exposed: Breach, Implications, and Remediation
Explore the critical NVRAM SSID-like vulnerabilities affecting Netgear products, leading to denial of service and command injection risks. Learn about the causes, affected models, and implications for users.

